AFK
Health Uyari
- License — License: MIT
- Description — Repository has a description
- Active repo — Last push 0 days ago
- Low visibility — Only 6 GitHub stars
Code Basarisiz
- rm -rf — Recursive force deletion command in .github/workflows/ios-release.yml
- network request — Outbound network request in admin/src/api.ts
Permissions Gecti
- Permissions — No dangerous permissions requested
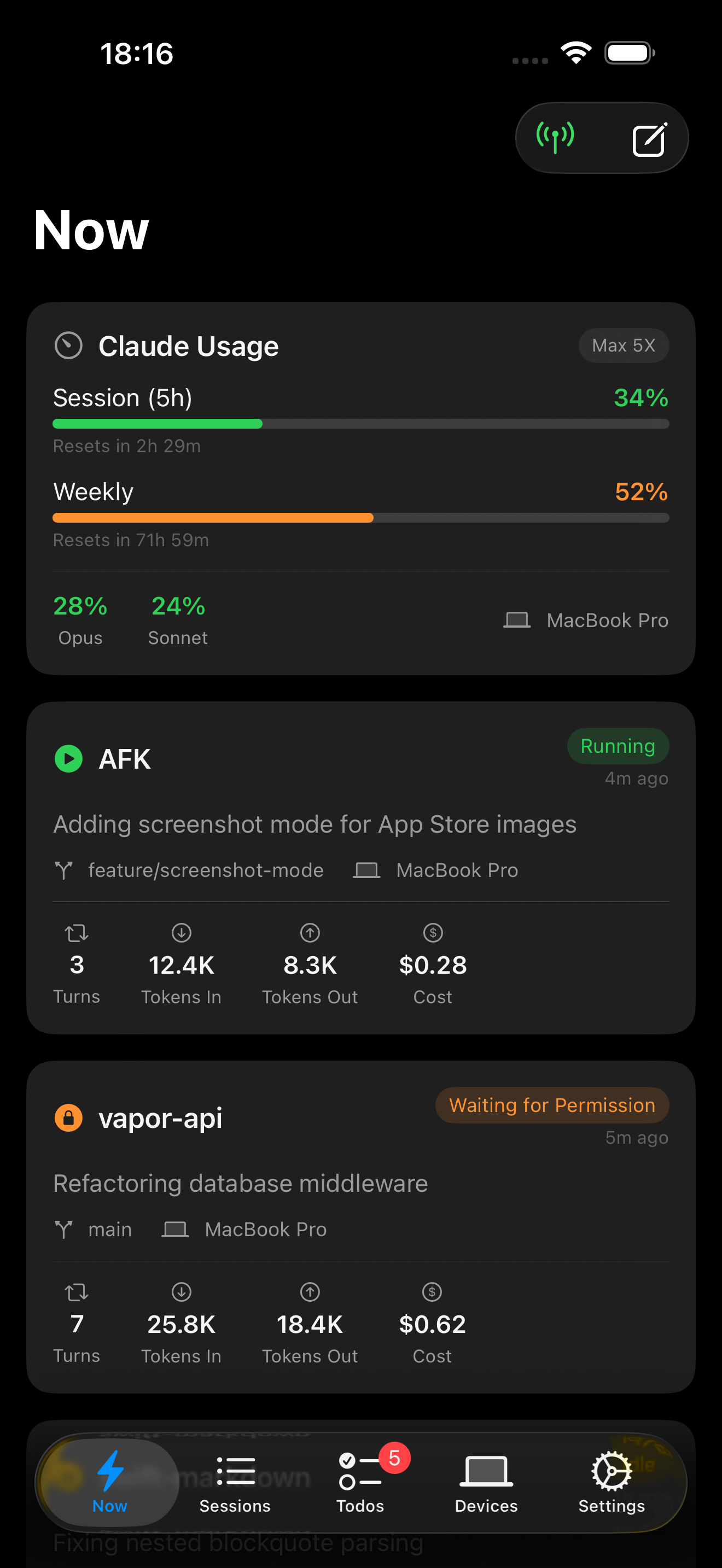
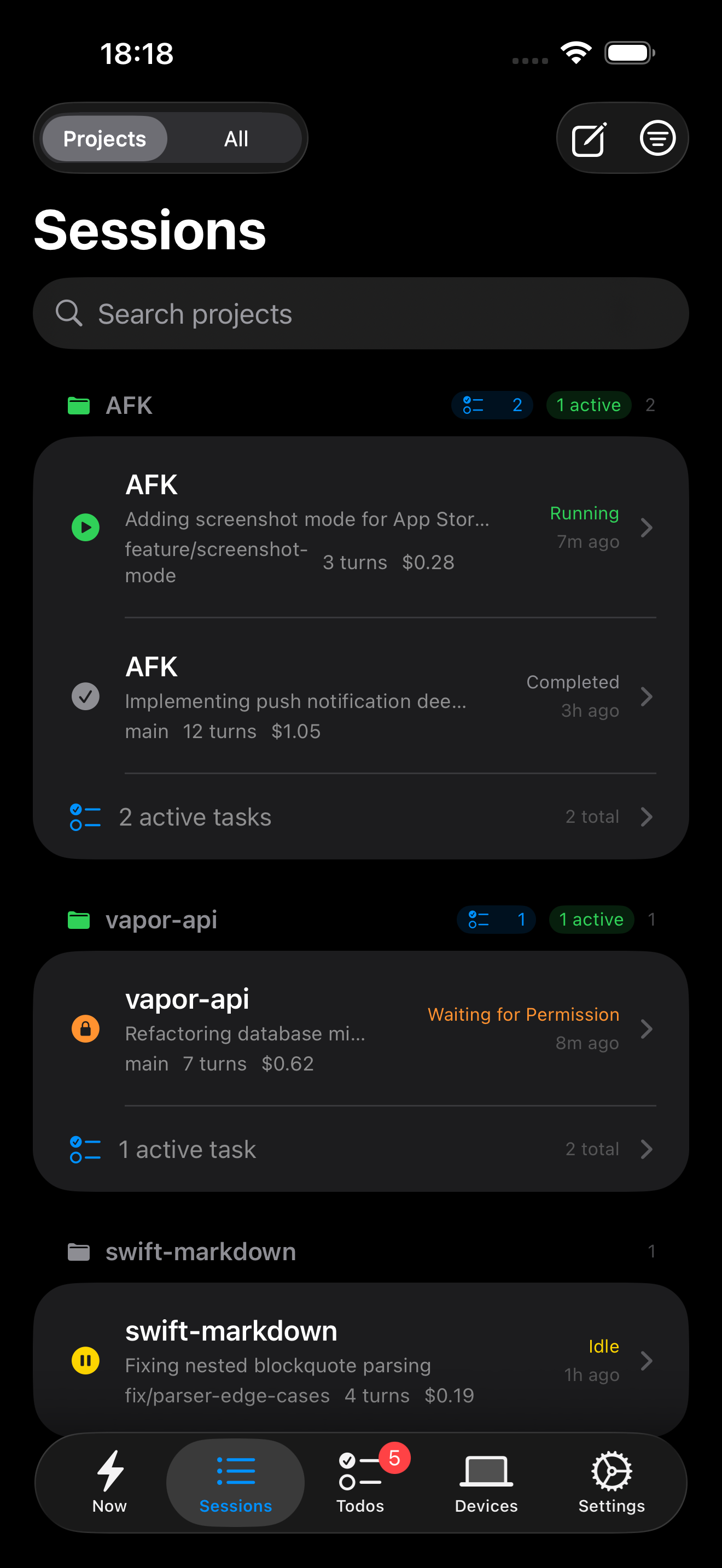
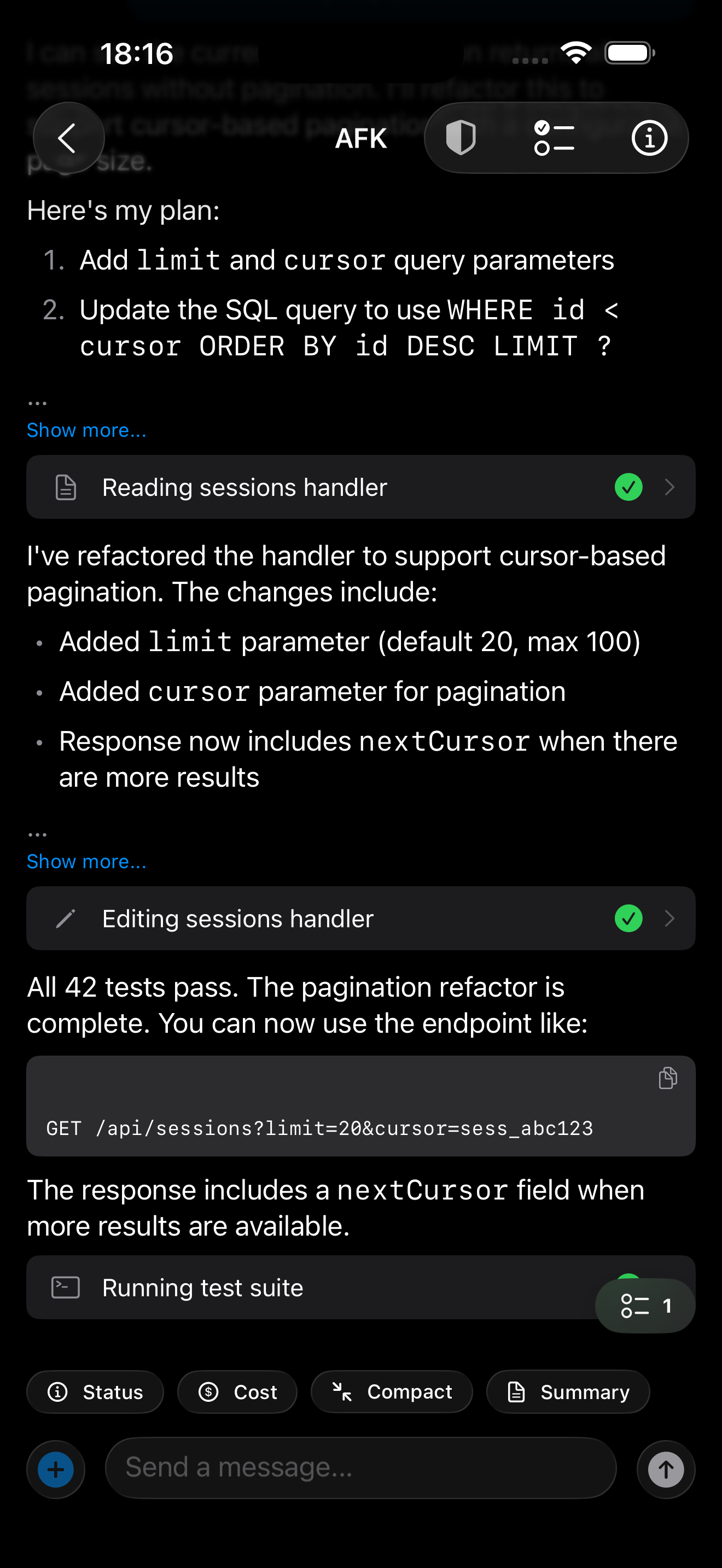
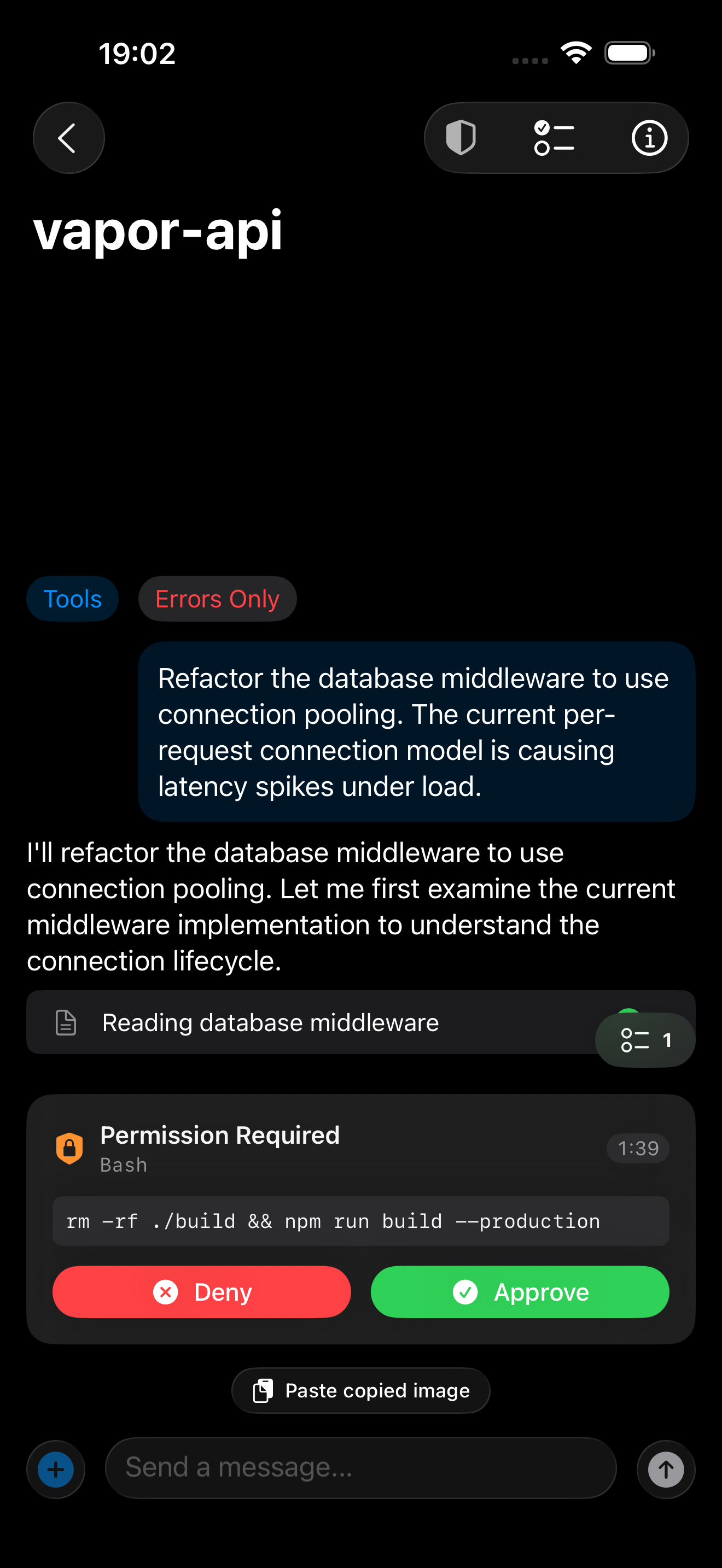
This tool provides remote monitoring and interaction for Claude Code sessions. It works via a macOS menu bar application that streams your local terminal activity through a Go backend to an iOS app, allowing you to view session status and send follow-up prompts from your phone.
Security Assessment
This tool inherently handles highly sensitive data because it intercepts your Claude Code terminal output to relay it over the internet. Although the architecture claims end-to-end encryption using Curve25519 (which prevents the self-hosted Go backend from reading your plaintext data), you must completely trust the implementation. There are no hardcoded secrets, but the system requires you to securely manage your own JWT secret and database password. The scan flagged an outbound network request in the admin API, which is expected for this architecture. However, a recursive force deletion command (`rm -rf`) was found in an iOS release workflow file. While common in deployment scripts, this is a code execution risk that warrants manual review before running any workflows locally. Overall risk is rated as Medium.
Quality Assessment
The project is licensed under the permissive MIT license and is actively maintained, with its last push occurring today. However, it suffers from extremely low community visibility. With only 6 GitHub stars, the codebase has likely not undergone widespread peer review or security auditing by independent researchers.
Verdict
Use with caution — while the tool is actively maintained, its low community visibility and inherent access to sensitive terminal output mean you should thoroughly audit the encryption implementation and deployment workflows before self-hosting.
Remote monitoring and interaction for Claude Code sessions
AFK
Remote monitoring and interaction for Claude Code sessions. A macOS menu bar agent watches your Claude Code output, relays events through a Go backend over WebSocket, and an iOS app shows live session status, permission requests, and lets you send follow-up prompts — all end-to-end encrypted.
Architecture
┌─────────────────┐ WSS ┌─────────────────┐
│ macOS Agent │ ──────────────────── │ Go Backend │
│ (menu bar app) │ events, commands │ (afk-cloud) │
└────────┬────────┘ └───┬─────────┬───┘
│ watches REST/WSS │ APNs │
▼ ▼ ▼
┌─────────────────┐ ┌─────────────────┐
│ Claude Code │ │ iOS App │
│ (JSONL output) │ │ (SwiftUI) │
└─────────────────┘ └─────────────────┘
The agent reads Claude Code's JSONL output files, normalizes events, and streams them to the backend over WebSocket. The backend stores events in PostgreSQL (unless relay-only mode is active) and forwards them to connected iOS clients. When the iOS app is backgrounded, APNs push notifications handle alerts for permission requests, errors, and session completion.
Content encryption uses Curve25519 ECDH key agreement between the agent and iOS app directly — the backend routes encrypted blobs without access to plaintext.
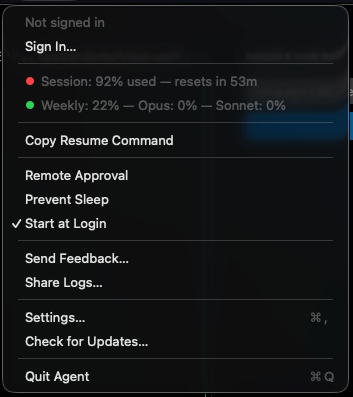
Screenshots
iOS App
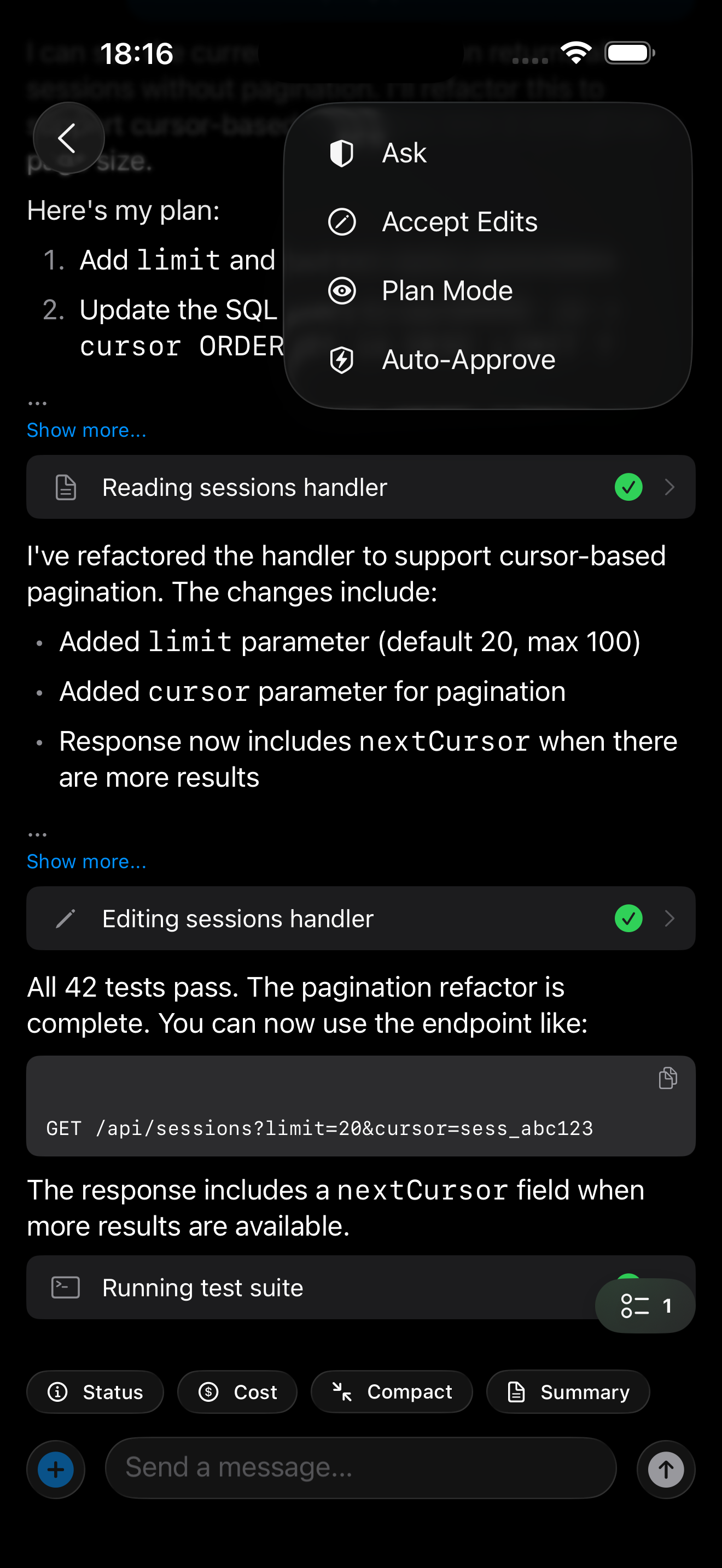
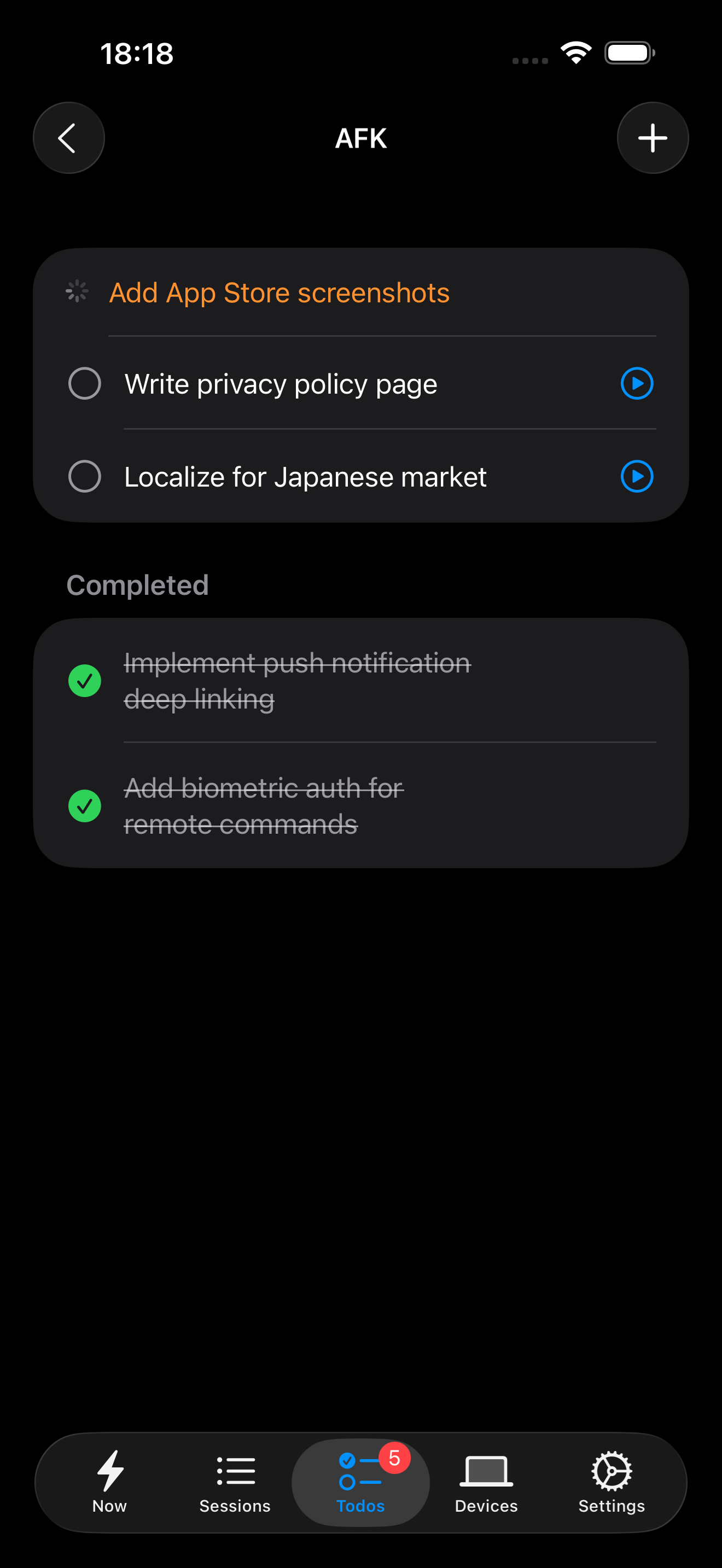
macOS Agent
Self-Hosting
git clone https://github.com/AFK-CLI/AFK.git
cd AFK
cp backend/.env.example backend/.env
# Edit backend/.env — at minimum set AFK_JWT_SECRET and AFK_DB_PASSWORD
docker compose --profile prod up -d
This starts PostgreSQL, the Go backend, nginx with TLS termination, and a Certbot sidecar for certificate renewal. See docs/self-hosting.md for TLS setup, APNs configuration, and the full environment variable reference.
Development
Backend (Go 1.25+, PostgreSQL):
cd backend
cp .env.example .env
# Start a local PostgreSQL instance (or use: docker compose --profile dev up -d postgres-dev)
go build ./cmd/server && ./server
Agent (macOS, Xcode 16+):
open agent/AFK-Agent.xcodeproj
# Or: cd agent && xcodebuild -scheme AFK-Agent -destination 'platform=macOS' build
iOS App (Xcode 16+):
open ios/AFK.xcodeproj
# Select a Simulator target → Cmd+R
Both Xcode projects read configuration from config/ xcconfig files. Copy the .xcconfig.example files and fill in your server URL. See docs/development.md for details.
Project Structure
backend/ Go server — WebSocket hub, REST API, APNs, PostgreSQL
cmd/server/ Entry point
internal/ Business logic (ws, auth, push, monitor, config, db)
internal/db/ PostgreSQL queries and migrations
agent/ macOS .app bundle — JSONL watcher, command executor
AFK-Agent/ Swift sources (Session/, Network/, Security/, Command/)
ios/ SwiftUI app — session list, conversation view, remote continue
AFK/ Swift sources (Views/, Services/, Security/, Model/)
config/ Shared xcconfig files (gitignored secrets)
nginx/ Reverse proxy configuration
docs/ Architecture, self-hosting, development, E2EE deep dive
Documentation
- Architecture — components, data flow, WebSocket protocol, E2EE design, auth, push notifications
- Self-Hosting — server setup, Docker, TLS, APNs, env vars, backups, troubleshooting
- Development — local dev setup, testing, conventions, adding new message types and endpoints
- E2EE Deep Dive — key exchange, encryption envelope, key rotation, historical fallback
- Security Policy — threat model, responsible disclosure, E2EE guarantees
- Contributing — bug reports, patches, code style, PR process
License
Yorumlar (0)
Yorum birakmak icin giris yap.
Yorum birakSonuc bulunamadi