tooltrust-scanner
Health Uyari
- License — License: MIT
- Description — Repository has a description
- Active repo — Last push 0 days ago
- Low visibility — Only 7 GitHub stars
Code Gecti
- Code scan — Scanned 12 files during light audit, no dangerous patterns found
Permissions Gecti
- Permissions — No dangerous permissions requested
Bu listing icin henuz AI raporu yok.
Security scanner for AI agent tool definitions
ToolTrust Scanner
Scan MCP servers for prompt injection, data exfiltration, and privilege escalation before your AI agent blindly trusts them.
🚨 Urgent Security Update (March 24, 2026)
ToolTrust now detects and blocks the LiteLLM / TeamPCP supply chain exploit. If you are adding MCP servers that rely on litellm (v1.82.7/8), ToolTrust will trigger a CRITICAL Grade F warning and block installation to protect your SSH/AWS keys.
Live UI
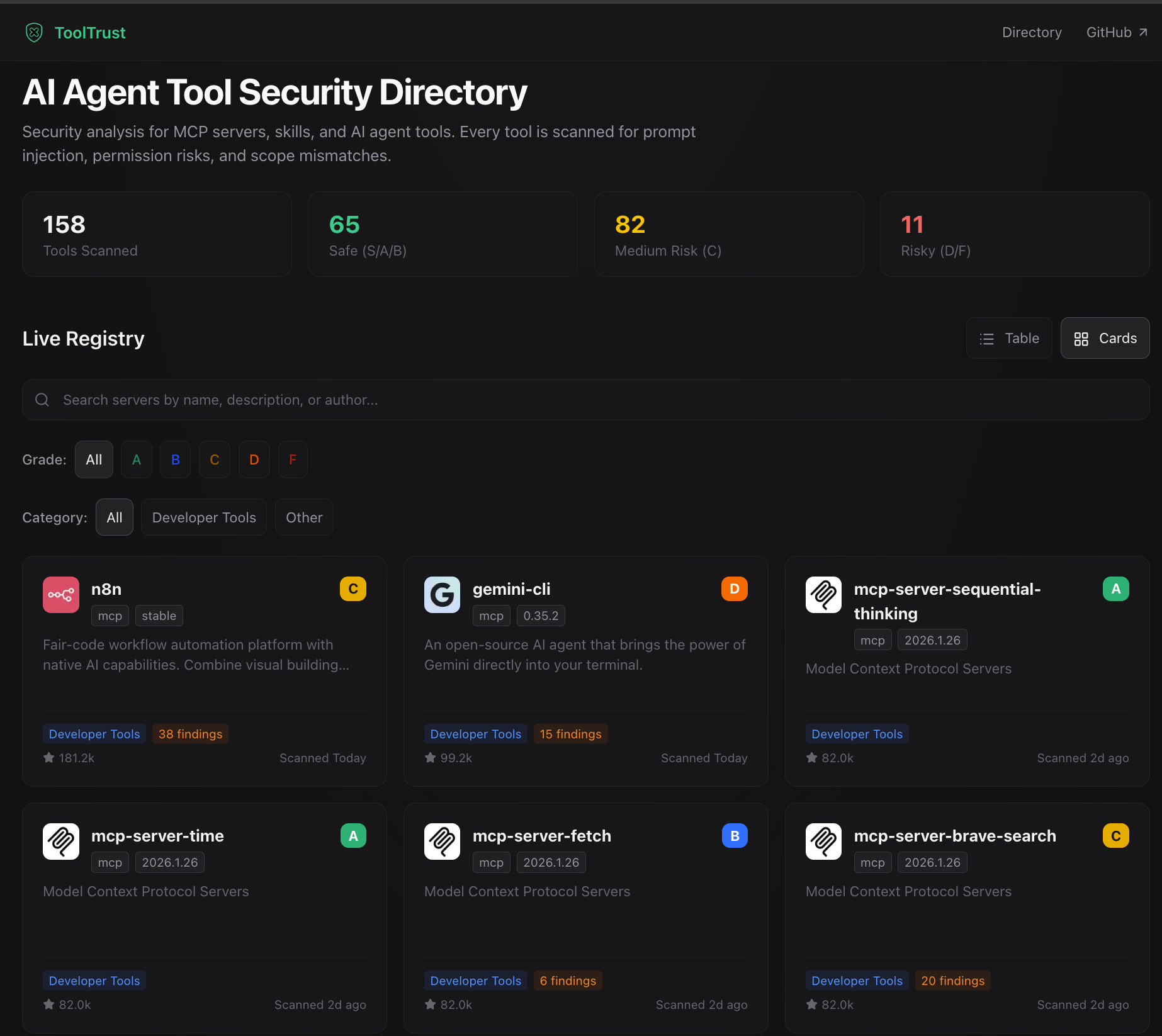
- Browse the public directory: https://www.tooltrust.dev/
- Look up historical grades for popular MCP servers
- Review findings in a browser before installing or trusting a server
What it looks like
Scan Summary: 14 tools scanned | 13 allowed | 1 need approval | 0 blocked
Tool Grades: A×13 C×1
Findings by Severity: HIGH×1 MEDIUM×14 LOW×1 (16 total)
Flagged Tools:
• search_files 🟡 GRADE C needs approval
[AS-002] High: Network access declared
[AS-011] Low: Missing rate-limit or timeout
Action now: Keep this tool on manual approval until the risky capabilities are reviewed.
🤖 Let your AI agent scan its own tools
Add ToolTrust as an MCP server in your .mcp.json and your agent can audit every tool it has access to:
Note: First run downloads a ~10MB Go binary from GitHub Releases. Subsequent runs use the cached binary.
{
"mcpServers": {
"tooltrust": {
"command": "npx",
"args": ["-y", "tooltrust-mcp"]
}
}
}
Then ask your agent to run:
tooltrust_scan_configto scan all configured MCP serverstooltrust_scan_serverto scan one specific server- Full MCP tool list: Usage guide
🔍 What it catches
- Prompt injection and tool poisoning hidden in descriptions
- Excessive permissions such as
exec,network,db, andfs - Supply-chain CVEs and known compromised package versions
- Privilege escalation and arbitrary code execution patterns
- Typosquatting, tool shadowing, and insecure secret handling
- Missing rate-limit, timeout, or retry configuration on risky tools
Full rule catalog: docs/RULES.md · tooltrust.dev
More ways to use ToolTrust
- CLI install, examples, and flags: Usage guide
- Scan-before-install workflow: Gate docs
- CI / GitHub Actions examples: CI integration
- Pre-commit / alias setup: Pre-hook integration
Usage guide · Developer guide · Contributing · Changelog · Security · License: MIT © 2026 AgentSafe-AI
Yorumlar (0)
Yorum birakmak icin giris yap.
Yorum birakSonuc bulunamadi



