oasm-assistant
Health Pass
- License — License: MIT
- Description — Repository has a description
- Active repo — Last push 0 days ago
- Community trust — 21 GitHub stars
Code Pass
- Code scan — Scanned 12 files during light audit, no dangerous patterns found
Permissions Pass
- Permissions — No dangerous permissions requested
This tool is an AI-powered platform that automates external attack surface management. It utilizes a multi-agent architecture to provide threat intelligence, vulnerability analysis, incident response, and compliance checking.
Security Assessment
The tool makes external network requests for threat monitoring, web protection, and integrating with various Large Language Models (LLMs). It relies on a PostgreSQL database with vector search capabilities for its RAG system, which handles potentially sensitive security and asset data. Users must configure their own API keys and environment variables via a local `.env` file. A light code scan of 12 files found no hardcoded secrets, dangerous execution patterns, or requests for risky permissions. Overall risk is rated as Low.
Quality Assessment
The project is highly active, with its last push occurring today. It is fully licensed under the standard MIT license. While the community trust level is relatively small with 21 GitHub stars, the provided documentation, architecture diagrams, and structured deployment model indicate a professional and well-maintained effort. However, users should be aware of an upcoming transition: the project will be renamed to "OASM AI Agent" in April 2026 and moved to a different monorepo.
Verdict
Safe to use.
Smart assistant for threat monitoring, attack prevention, and web protection.
⚠️ Important Notice
Starting from 2026-04-04, OASM Assistant will be renamed to OASM AI Agent and will be developed directly at:
https://github.com/oasm-platform/open-asm/tree/main/core-api/src/modules/agents
🤖 OASM ASSISTANT
AI-Powered External Attack Surface Management
Overview
OASM Assistant is an AI-powered security platform that automates external attack surface management using multi-agent architecture with LangGraph.
Key Features
🤖 Multi-Agent AI System - Specialized agents for security tasks
- Threat Intelligence Agent - IOC correlation, attack prediction, threat monitoring
- Analysis Agent - Vulnerability assessment, compliance checking (OWASP, CWE, PCI-DSS, ISO 27001, etc)
- Incident Responder Agent - Attack detection, automated response, forensic analysis
- Orchestrator Agent - Workflow coordination, natural language interface
🔍 Threat Intelligence - Real-time monitoring and analysis
🛡️ Vulnerability Management - Automated scanning and prioritization
📊 Compliance Checking - OWASP, CWE, PCI-DSS, ISO 27001, etc
⚡ Incident Response - Automated detection and response
🔧 Utility Tools - Domain Classifier, Nuclei Template Generator, Issue Resolver
Quick Start
# Clone repository
git clone https://github.com/oasm-platform/oasm-assistant.git
cd oasm-assistant
# Configure
cp .env.example .env
nano .env # Edit environment variables
# Start services
docker compose up -d oasm-assistant-postgresql oasm-assistant-app oasm-assistant-searxng oasm-assistant-ollama
# Pull model for Ollama (if using Ollama LLM)
docker exec -it oasm-assistant-ollama ollama pull llama3
Architecture
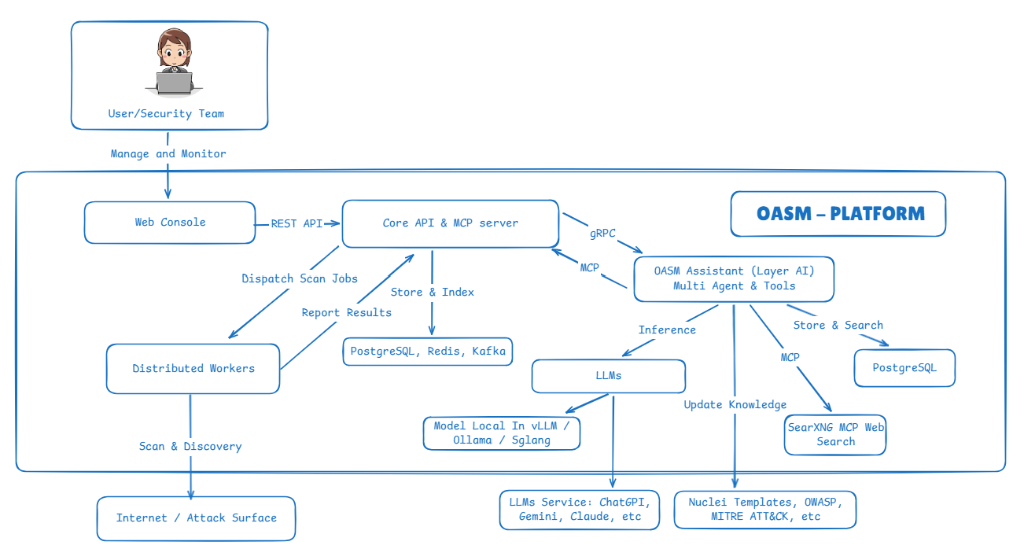
🤖 OASM ASSISTANT (AI Layer)
Intelligent automation layer built on top of OASM Platform
Components:
- Multi-Agent System - Threat Intel • Analysis • Incident Response • Orchestrator
- LLM Providers - Local (Ollama, vLLM, SGLang) • Cloud (OpenAI, Claude, Gemini)
- AI Tools - RAG System (pgvector) • SearXNG • Domain Classifier • Nuclei Generator • Issue Resolver
Integration:
- gRPC - High-performance communication with Core API
- MCP Protocol - Real-time asset context and knowledge retrieval
- PostgreSQL - Vector search for RAG (Retrieval Augmented Generation)
⚙️ OASM CORE (Management Platform)
Central platform for external attack surface management → View Core Platform
Components:
- Web Console - Management dashboard
- Core API & MCP Server - REST, gRPC, MCP protocols
- Database - PostgreSQL, Redis, Kafka
- Distributed Workers - Security scanning execution
External Resources:
- Internet/Attack Surface - Target systems
- Knowledge Base - Nuclei Templates, OWASP, MITRE ATT&CK, etc
Documentation
📚 Getting Started
- Installation Guide - Docker setup, GPU configuration
- Configuration Guide - Environment variables, provider setup
- LLM Deployment - Complete LLM & embedding setup
🔧 Advanced
- Architecture (coming soon)
- API Reference (coming soon)
- Development Guide (coming soon)
Technology Stack
- AI Framework: LangGraph, LangChain
- LLM Providers: Ollama, vLLM, SGLang, OpenAI, Anthropic, Google
- RAG: pgvector (vector search), BM25 (keyword search)
- Communication: gRPC, MCP (Model Context Protocol)
- Storage: PostgreSQL with pgvector extension
License
MIT License - see LICENSE file.
Disclaimer
For defensive security only. Use only on systems you own or have permission to test.
Built by Team OASM-Platform • Documentation • Issues
Reviews (0)
Sign in to leave a review.
Leave a reviewNo results found


