clawgod
skill
Fail
Health Pass
- License — License: GPL-3.0
- Description — Repository has a description
- Active repo — Last push 0 days ago
- Community trust — 465 GitHub stars
Code Fail
- rm -rf — Recursive force deletion command in install.sh
- process.env — Environment variable access in install.sh
- fs module — File system access in install.sh
Permissions Pass
- Permissions — No dangerous permissions requested
Purpose
This tool is a runtime patch for the official Claude Code CLI. It modifies the application to unlock hidden internal features, enable multi-agent swarms, and remove built-in safety restrictions, such as refusals for security testing and forced confirmations for destructive actions.
Security Assessment
Overall Risk: High. The tool is a Shell script that modifies installed software by heavily accessing the file system. The installer script contains a recursive force deletion command (`rm -rf`), which, while common for uninstalling, poses a significant risk if the script is altered or behaves unexpectedly. Furthermore, the tool explicitly disables security guardrails, such as the CYBER_RISK_INSTRUCTION refusal mechanism and cautious action checks. Using this patch allows the AI to perform potentially destructive operations and generate exploits without standard safety nets. The installation method relies on piping remote scripts directly into bash, which is a common vector for executing unverified code. No hardcoded secrets were detected.
Quality Assessment
The project is actively maintained, with its last push occurring less than a day ago. It has garnered 465 GitHub stars, indicating a notable level of community trust and usage. The codebase is distributed under the GPL-3.0 license.
Verdict
Use with caution — This tool executes deep system modifications and disables core AI safety restrictions, meaning it should only be used by experienced developers who fully understand the operational and account-related risks.
This tool is a runtime patch for the official Claude Code CLI. It modifies the application to unlock hidden internal features, enable multi-agent swarms, and remove built-in safety restrictions, such as refusals for security testing and forced confirmations for destructive actions.
Security Assessment
Overall Risk: High. The tool is a Shell script that modifies installed software by heavily accessing the file system. The installer script contains a recursive force deletion command (`rm -rf`), which, while common for uninstalling, poses a significant risk if the script is altered or behaves unexpectedly. Furthermore, the tool explicitly disables security guardrails, such as the CYBER_RISK_INSTRUCTION refusal mechanism and cautious action checks. Using this patch allows the AI to perform potentially destructive operations and generate exploits without standard safety nets. The installation method relies on piping remote scripts directly into bash, which is a common vector for executing unverified code. No hardcoded secrets were detected.
Quality Assessment
The project is actively maintained, with its last push occurring less than a day ago. It has garnered 465 GitHub stars, indicating a notable level of community trust and usage. The codebase is distributed under the GPL-3.0 license.
Verdict
Use with caution — This tool executes deep system modifications and disables core AI safety restrictions, meaning it should only be used by experienced developers who fully understand the operational and account-related risks.
This is NOT a third-party Claude Code client. ClawGod is a runtime patch applied on top of the official Claude Code. It works with any version — as Claude Code updates, the patch continues to take effect
README.md
ClawGod
God mode for Claude Code.
This is NOT a third-party Claude Code client. ClawGod is a runtime patch applied on top of the official Claude Code. It works with any version — as Claude Code updates, the patch continues to take effect.
Install
macOS / Linux:
curl -fsSL https://github.com/0Chencc/clawgod/releases/latest/download/install.sh | bash
Windows (PowerShell):
irm https://github.com/0Chencc/clawgod/releases/latest/download/install.ps1 | iex
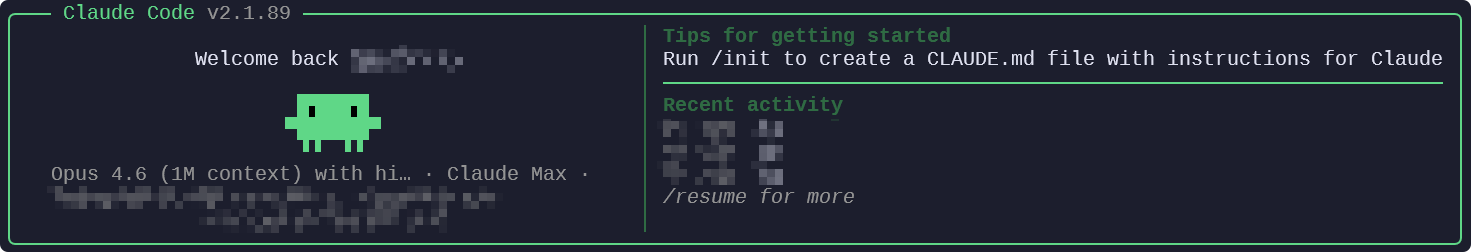
Green logo = patched. Orange logo = original.
What it does
Feature Unlocks
| Patch | What you get |
|---|---|
| Internal User Mode | 24+ hidden commands (/share, /teleport, /issue, /bughunter...), debug logging, API request dumps |
| GrowthBook Overrides | Override any feature flag via config file |
| Agent Teams | Multi-agent swarm collaboration, no flags needed |
| Computer Use | Screen control without Max/Pro subscription (macOS) |
| Ultraplan | Multi-agent planning via Claude Code Remote |
| Ultrareview | Automated bug hunting via Claude Code Remote |
Restriction Removals
| Patch | What's removed |
|---|---|
| CYBER_RISK_INSTRUCTION | Security testing refusal (pentesting, C2, exploits) |
| URL Restriction | "NEVER generate or guess URLs" instruction |
| Cautious Actions | Forced confirmation before destructive operations |
| Login Notice | "Not logged in" startup reminder |
Visual
| Patch | Effect |
|---|---|
| Green Theme | Brand color → green. Patched at a glance |
| Message Filters | Shows content hidden from non-Anthropic users |
Commands
claude # Patched Claude Code
claude.orig # Original unpatched version
Update
Re-run the installer to get the latest version with patches re-applied:
macOS / Linux:
curl -fsSL https://github.com/0Chencc/clawgod/releases/latest/download/install.sh | bash
Windows:
irm https://github.com/0Chencc/clawgod/releases/latest/download/install.ps1 | iex
Uninstall
macOS / Linux:
curl -fsSL https://github.com/0Chencc/clawgod/releases/latest/download/install.sh | bash -s -- --uninstall
Windows:
irm https://github.com/0Chencc/clawgod/releases/latest/download/install.ps1 -OutFile install.ps1; .\install.ps1 -Uninstall
Requirements
- Node.js >= 18 + npm
- Claude Code account (
claude auth login)
License
GPL-3.0 — Not affiliated with Anthropic. Use at your own risk.
Reviews (0)
Sign in to leave a review.
Leave a reviewNo results found