radar
Health Pass
- License — License: Apache-2.0
- Description — Repository has a description
- Active repo — Last push 0 days ago
- Community trust — 1327 GitHub stars
Code Fail
- rm -rf — Recursive force deletion command in .github/workflows/release.yml
- rm -rf — Recursive force deletion command in .goreleaser.yaml
Permissions Pass
- Permissions — No dangerous permissions requested
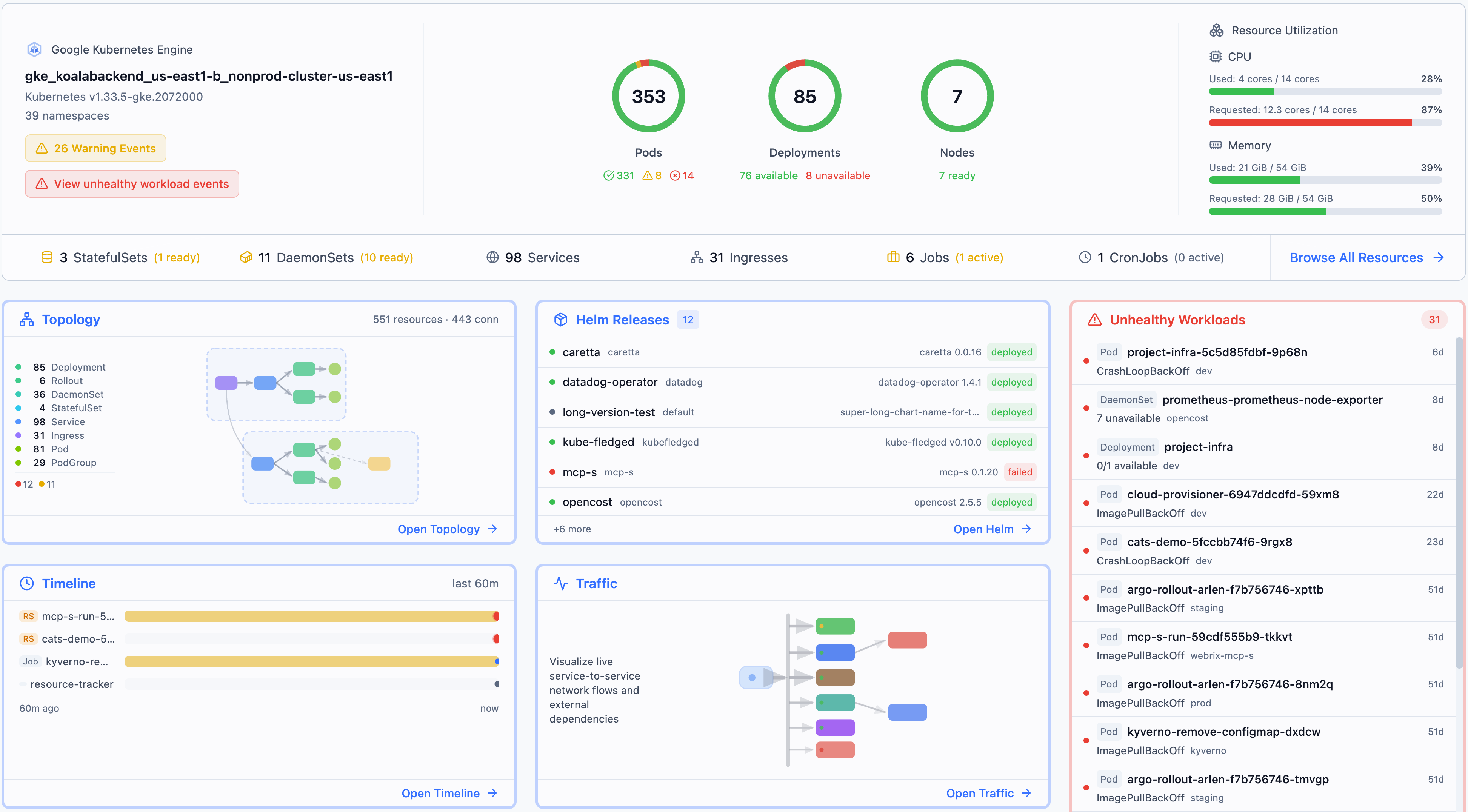
This tool provides modern, local-first Kubernetes visibility. It allows you to visualize cluster topology, browse resources, stream logs, and manage Helm releases directly from your laptop or via an integrated AI-ready MCP server.
Security Assessment
Overall Risk: Medium. Because this is a Kubernetes management tool, it inherently requires access to highly sensitive data, including your cluster architecture, metadata, and pod logs. It operates by communicating directly with the Kubernetes API, constituting a significant network integration. While no hardcoded secrets or dangerous runtime permissions were found, the audit flagged the use of `rm -rf` in the GitHub release workflow and GoReleaser configuration. These commands are typical build environment cleanup operations rather than active security vulnerabilities. However, the quick installation method heavily relies on piping a remote shell script directly to bash (`curl | bash`), which can be a security risk if the repository or domain is ever compromised.
Quality Assessment
The project is highly active and exhibits strong community trust, boasting over 1,300 GitHub stars and receiving code updates as recently as today. It uses the standard and permissive Apache-2.0 license. The developers actively maintain the application, as demonstrated by comprehensive installation options for multiple platforms and a transparent release pipeline. The project is clearly not abandoned and is well-documented.
Verdict
Use with caution — the tool is a high-quality and actively maintained project, but you should always inspect the remote bash script before executing it in your terminal, and strictly limit the Kubernetes API permissions it is allowed to use.
Modern Kubernetes visibility. Topology, event timeline, and service traffic — plus resource browsing and Helm management.
Radar
[!IMPORTANT]
📣 Radar is launching on Product Hunt this Sunday!
Follow Radar on PH ↗ · We have a new Discord ↗
Modern Kubernetes visibility.
Local-first. No account. No cloud dependency. Blazing Fast.
🌐 radarhq.io · Docs · Releases
Topology, event timeline, and service traffic — plus resource browsing, Helm management, and GitOps support for FluxCD and ArgoCD.
Visualize your cluster topology, browse resources, stream logs, exec into pods, inspect container image filesystems, manage Helm releases, monitor GitOps workflows (FluxCD & ArgoCD), and forward ports - all from a single binary with zero cluster-side installation.
Install and run in 30 seconds:
curl -fsSL https://raw.githubusercontent.com/skyhook-io/radar/main/install.sh | bash && kubectl radar
Why Radar?
- Zero install on your cluster — runs on your laptop, talks to the K8s API directly
- Single binary — no dependencies, no agents, no CRDs
- Blazing fast - smart caching, progressive loading, parallelization and other optimizations
- Airgapped-ready — no external network calls, works in isolated environments
- Real-time — watches your cluster via informers, pushes updates to the browser via SSE
- Works everywhere — GKE, EKS, AKS, minikube, kind, k3s, or any conformant cluster
- AI-ready — built-in MCP server lets AI assistants query your cluster through Radar
- In-cluster option — deploy with Helm for shared team access with RBAC-scoped permissions
Installation
Quick Install:
curl -fsSL https://raw.githubusercontent.com/skyhook-io/radar/main/install.sh | bash
Homebrew:
brew install skyhook-io/tap/radar
Then run: kubectl radar (or simply radar)
CLI
Krew (kubectl plugin manager):
kubectl krew install radar
Scoop (Windows):
scoop bucket add skyhook https://github.com/skyhook-io/scoop-bucket
scoop install radar
PowerShell (Windows):
irm https://raw.githubusercontent.com/skyhook-io/radar/main/install.ps1 | iex
Direct download — GitHub Releases for macOS, Linux, or Windows.
Desktop App
Native desktop app — no terminal needed.
Homebrew (macOS):
brew install --cask skyhook-io/tap/radar-desktop
Debian/Ubuntu:
sudo apt install ./radar-desktop_*.deb
Fedora/RHEL:
sudo rpm -i radar-desktop_*.rpm
Scoop (Windows):
scoop bucket add skyhook https://github.com/skyhook-io/scoop-bucket
scoop install radar-desktop
Windows (direct download) — GitHub Releases.
In-Cluster Deployment
Deploy to your cluster for shared team access:
helm repo add skyhook https://skyhook-io.github.io/helm-charts
helm install radar skyhook/radar -n radar --create-namespace
See the In-Cluster Deployment Guide for ingress, authentication, and RBAC configuration.
Usage
# Opens browser automatically
kubectl radar
# Or simply
radar
CLI Flags
| Flag | Default | Description |
|---|---|---|
--kubeconfig |
~/.kube/config |
Path to kubeconfig file |
--kubeconfig-dir |
Comma-separated directories containing kubeconfig files | |
--namespace |
(all) | Initial namespace filter (supports multi-select in the UI; also used as RBAC fallback for namespace-scoped users) |
--port |
9280 |
Server port |
--no-browser |
false |
Don't auto-open browser |
--timeline-storage |
memory |
Timeline storage backend: memory or sqlite |
--timeline-db |
~/.radar/timeline.db |
Path to SQLite database (when using sqlite storage) |
--history-limit |
10000 |
Maximum events to retain in timeline |
--disable-exec |
false |
Disable terminal and debug shell |
--disable-helm-write |
false |
Disable Helm write operations |
--disable-local-terminal |
false |
Disable local terminal feature |
--prometheus-url |
(auto-discover) | Manual Prometheus/VictoriaMetrics URL (skips auto-discovery) |
--auth-mode |
none |
Authentication mode: none, proxy, or oidc (details) |
--no-mcp |
false |
Disable MCP server for AI tool integration |
--version |
Show version and exit |
See Configuration Guide for details on cluster connection precedence, multiple kubeconfig files, and context switching.
Views
Topology
Interactive graph showing how your Kubernetes resources are connected in real-time.
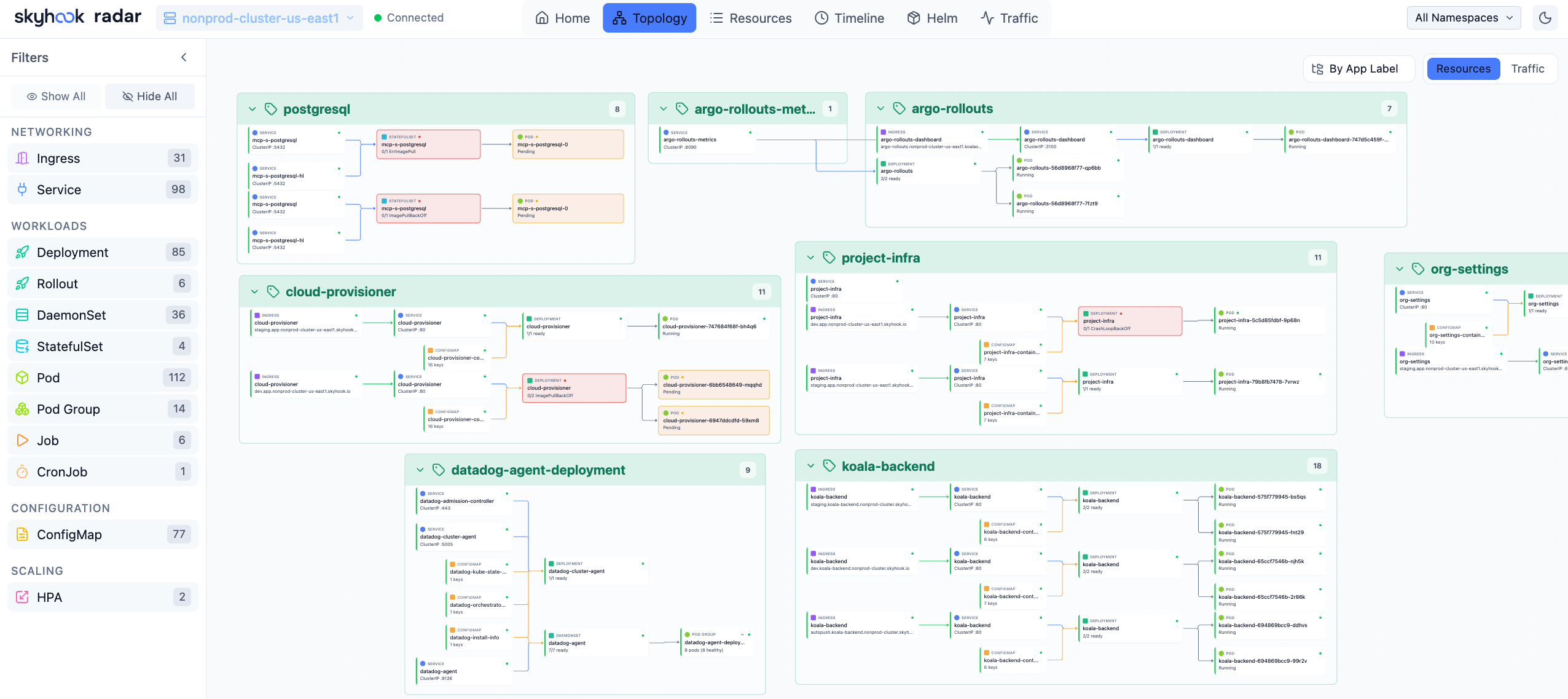
Topology View — Visualize resource relationships
- Two modes: Resources (full hierarchy) and Traffic (network flow path)
- Group by namespace, app label, or view ungrouped
- Filter by resource kind — click any node for full details
- Auto-layout powered by ELK.js, live updates via SSE
Resources
Table-based resource browser with smart columns per resource kind.
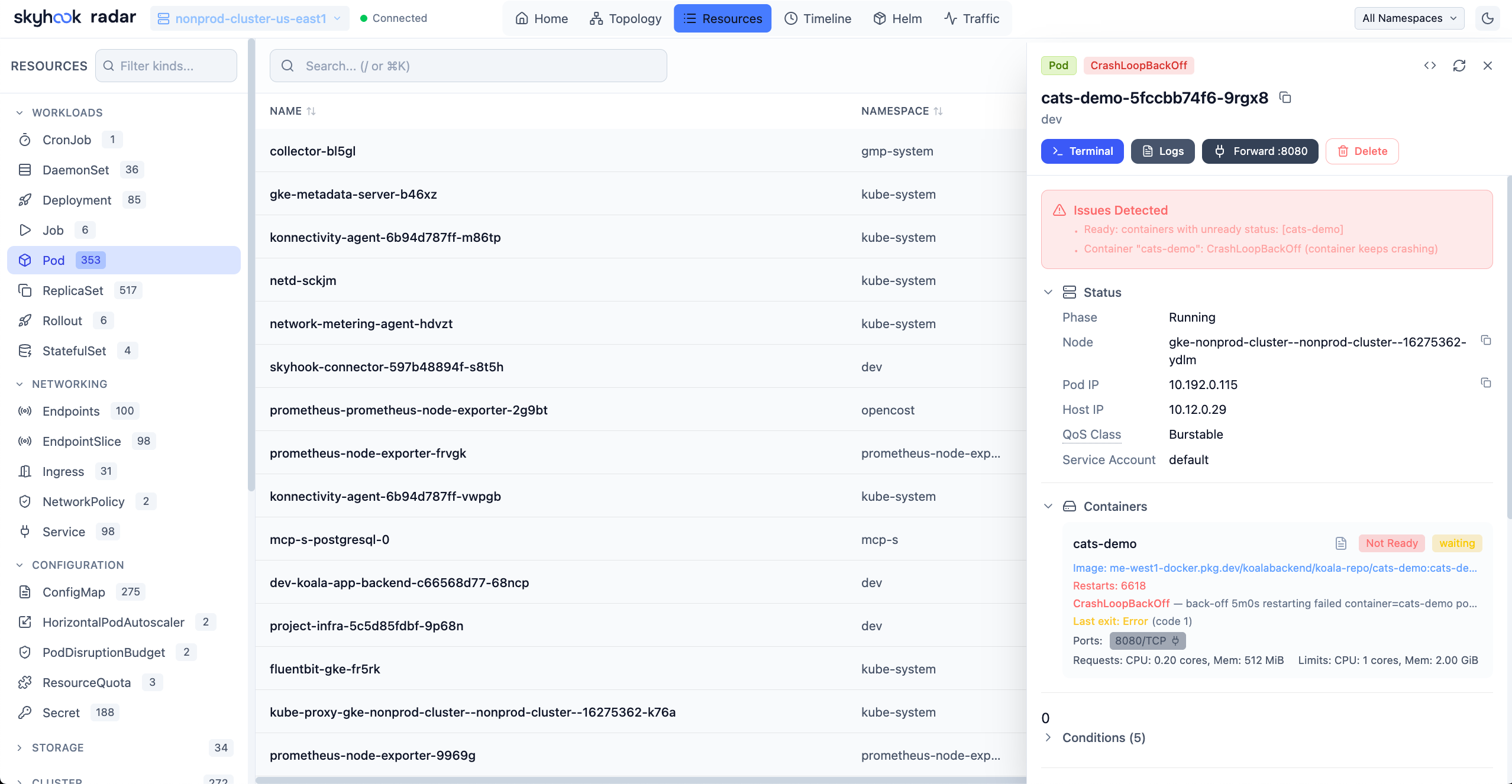
Resources View — Browse and filter all cluster resources
- Browse all resource types including CRDs
- Search by name, filter by status or problems (CrashLoopBackOff, ImagePullBackOff, etc.)
- Click any resource for YAML manifest, related resources, logs, and events
Image Filesystem Viewer
Inspect container image filesystems directly from the Pod view — no need to pull images locally or exec into containers.
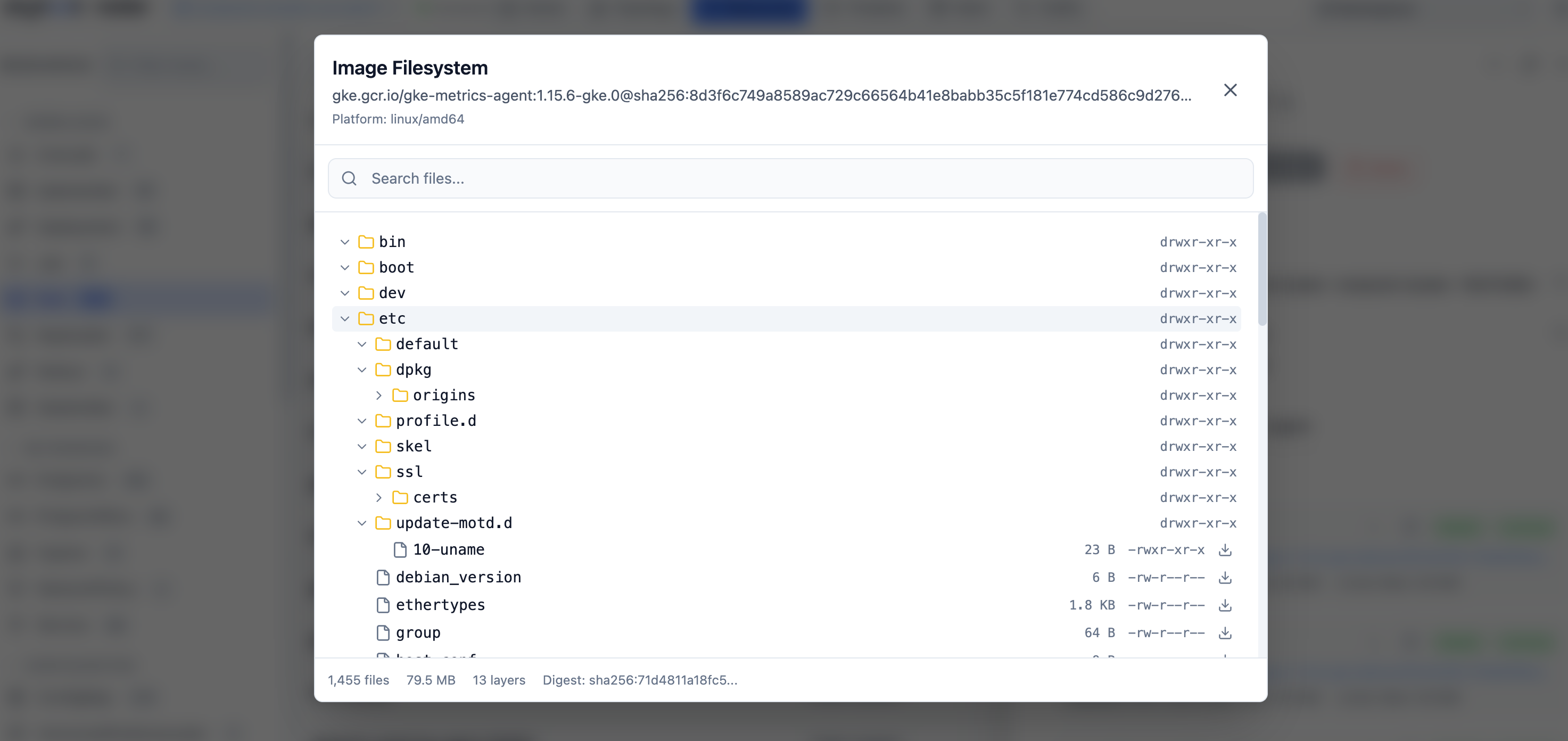
Image Filesystem Viewer — Browse container image contents
- Click any container image in a Pod to browse its complete filesystem
- Tree view with file sizes, permissions, and symlink targets
- Search files by name across the entire image
- Download individual files for inspection
- Works with public images (Docker Hub, Quay, GHCR) and private registries (GCR, ECR, ACR) using your cluster's ImagePullSecrets
- Disk-based layer caching for fast repeated access
Timeline
Unified timeline of Kubernetes events and resource changes.
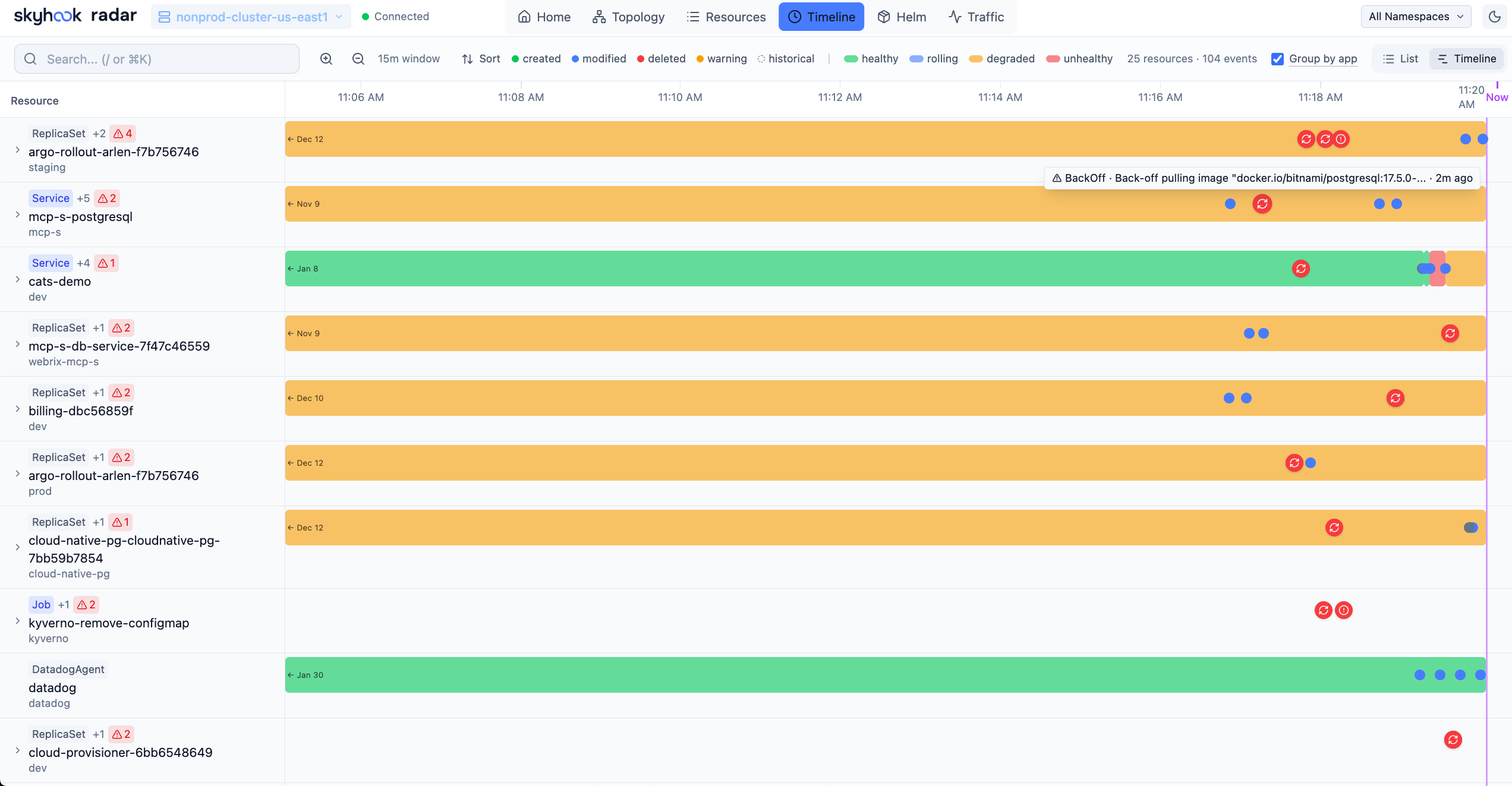
Timeline View — Track cluster activity in real-time
- Filter by event type (all or warnings only)
- Resource change diffs showing what changed (replicas, images, etc.)
- Real-time updates as new events occur
Helm
Manage Helm releases deployed in your cluster.
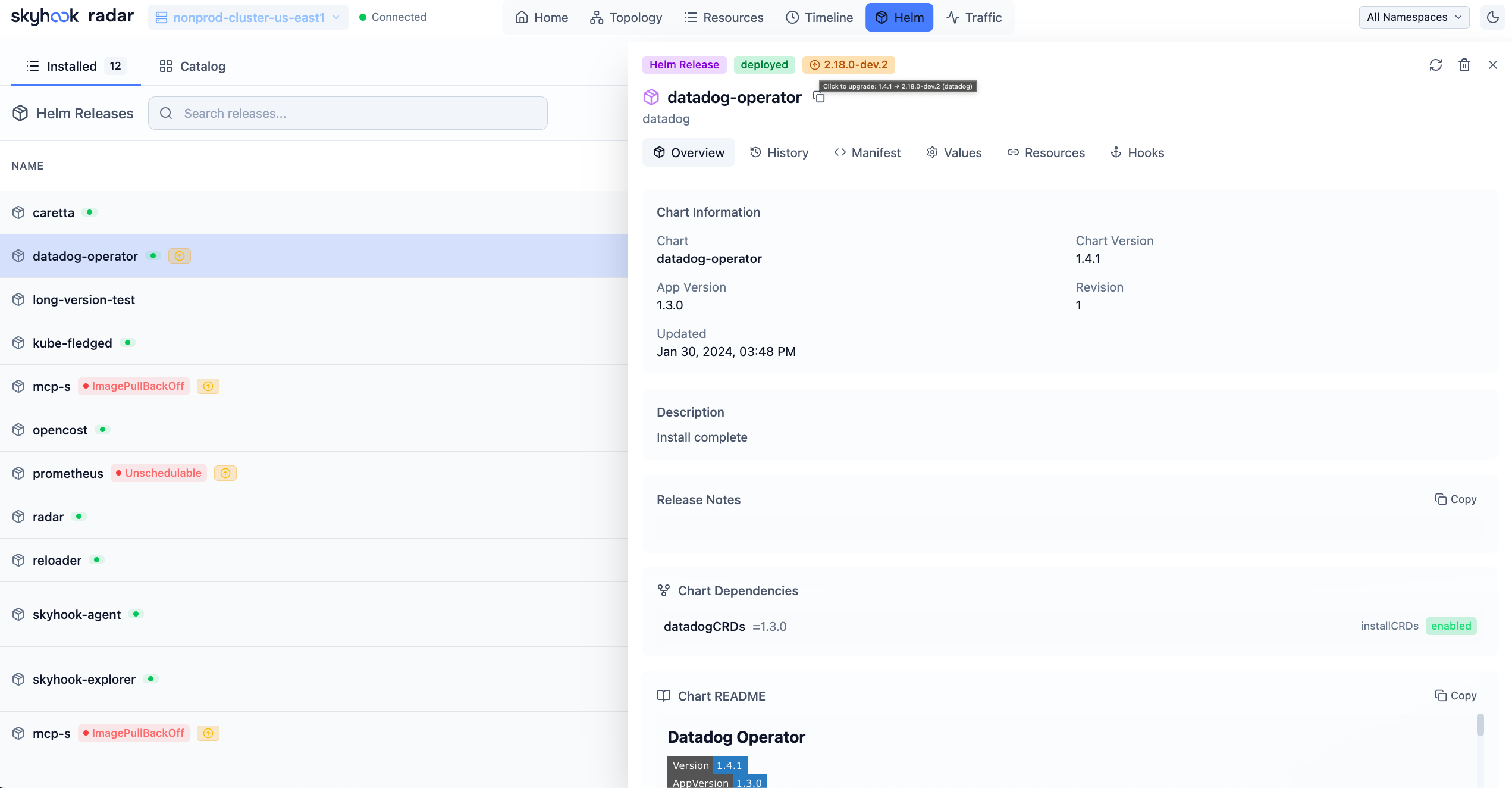
Helm View — Manage your Helm deployments
- View all releases across namespaces with status, chart version, and app version
- Inspect values, compare revisions, view release history
- Upgrade, rollback, or uninstall releases directly from the UI
TLS Certificate Management
View TLS certificate details and expiry dates across all namespaces — catch expiring certificates before they cause outages.
- Parses TLS secrets to show certificate subject, issuer, and validity period
- Dashboard-level certificate expiry overview
- Available from the resource detail view for any TLS-type Secret
GitOps
Monitor and manage FluxCD and ArgoCD resources with unified status views and actions.
- FluxCD: GitRepository, OCIRepository, HelmRepository, Kustomization, HelmRelease, Alert
- ArgoCD: Application, ApplicationSet, AppProject
- Real-time sync status, health indicators, and reconciliation countdowns
- Trigger reconciliation, suspend/resume resources, and view managed resource inventory
- Problem detection with clear alerts for degraded or out-of-sync resources
- Note: Topology connections between GitOps resources and managed workloads only appear when both are in the same cluster. FluxCD typically deploys to its own cluster. ArgoCD often manages remote clusters — connect Radar to the target cluster to see workloads, or to the ArgoCD cluster to see Application status.
Traffic
Visualize live network traffic between services using Hubble or Caretta.
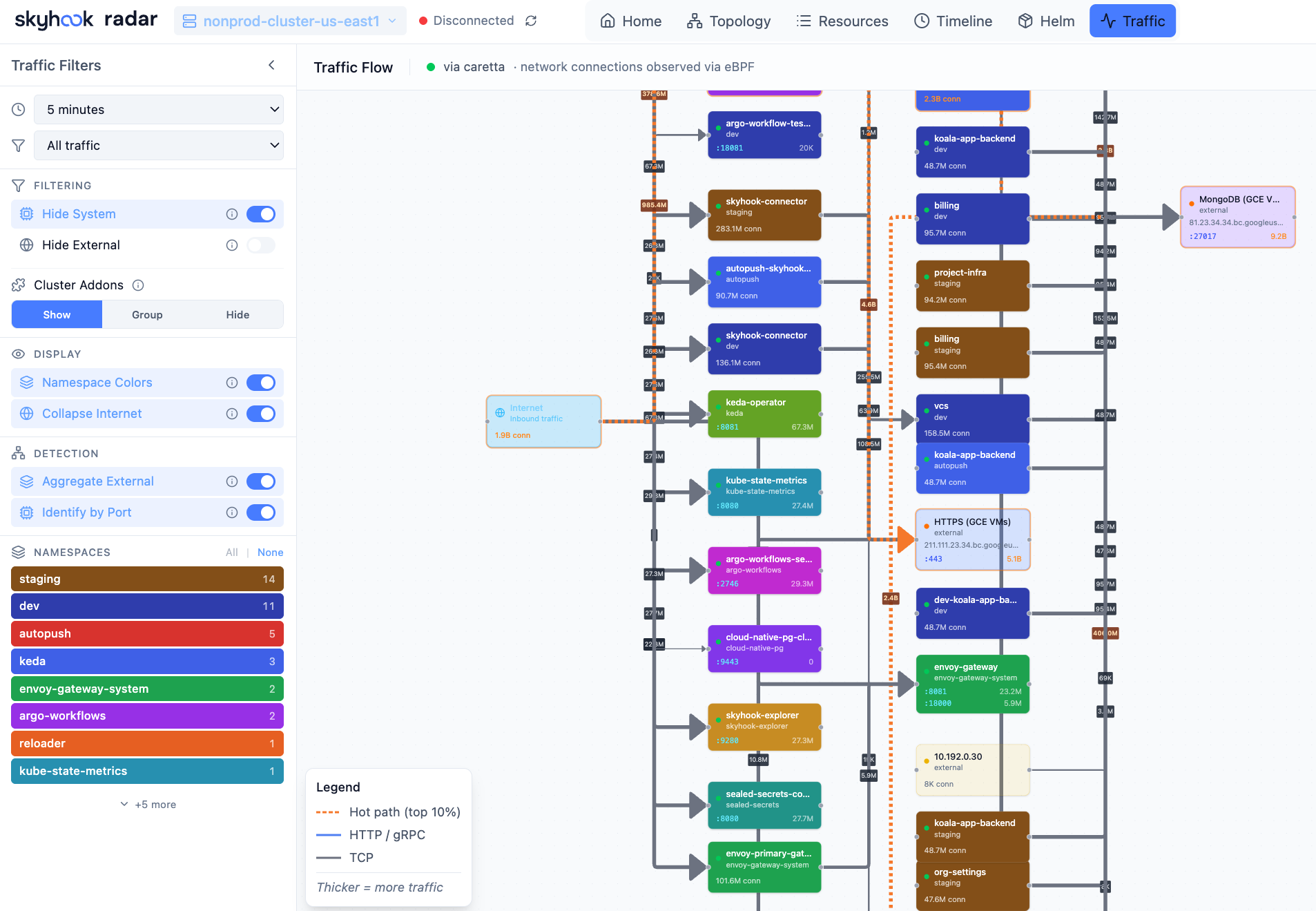
Traffic View — See how services communicate in real-time
- Auto-detects Hubble (Cilium), Caretta, or Istio as traffic data sources
- Animated flow graph showing requests per second between services
- Filter by namespace, protocol, or status code
- Setup wizard to install a traffic source if none is detected
Cost Insights
Track Kubernetes spending with OpenCost integration — no additional configuration needed.
- Cluster hourly and projected monthly cost, top namespaces by spend
- Cost trend charts with 6h/24h/7d range selector
- Namespace and workload-level cost breakdowns with efficiency scoring
- Node costs with instance type and region pricing
- Appears automatically when OpenCost metrics are detected in Prometheus
Cluster Audit
Proactive best-practices scanner with 31 checks across security, reliability, and efficiency — inspired by Polaris, Kubescape, Trivy, and NSA/CISA guidelines. Runs instantly against cached data with zero cluster-side installation.
- Security: privileged containers, privilege escalation, dangerous/insecure capabilities, host namespaces, container runtime socket mounts, sensitive host paths, secrets in ConfigMaps, auto-mounted service account tokens
- Reliability: missing probes, image tag
latest, single-replica deployments, missing PDB/topology spread, pod HA risk (all replicas on same node), orphan services/ingresses, deprecated API versions - Efficiency: missing CPU/memory requests and limits, orphan ConfigMaps/Secrets, resource utilization vs requests
- Grouped-by-resource and by-namespace views with search, category/severity/framework filters
- Each finding includes description and remediation guidance, with inline hide actions (per-check, per-category, per-namespace)
- Configurable: ignored namespaces (with wildcard patterns), disabled checks, persisted across sessions
- Framework labels: NSA/CISA, CIS benchmarks
- MCP tool (
get_cluster_audit) for AI-assisted cluster analysis
AI Integration (MCP) beta
Radar includes a built-in Model Context Protocol (MCP) server that lets AI assistants — Claude, Cursor, Copilot, and others — query your cluster through Radar.
Instead of raw kubectl output (verbose YAML that burns through LLM context windows), your AI gets pre-processed, token-optimized data: topology graphs, health assessments, deduplicated events, and filtered logs. Read tools are strictly read-only; write tools (restart, scale, sync) are clearly annotated and non-destructive.
Enabled by default. Disable with --no-mcp. See the MCP Guide for setup instructions.
Authentication
For shared in-cluster deployments, Radar supports optional user authentication with per-user Kubernetes RBAC.
- Proxy mode — works with oauth2-proxy, Pomerium, Cloudflare Access, or any auth proxy that sets forwarded headers
- OIDC mode — built-in login via Google, Okta, Dex, Keycloak, or any OIDC provider
- Per-user namespace scoping and write authorization via K8s impersonation
- UI adapts automatically — buttons only appear if the user has RBAC permission
No auth by default (local use). See the Authentication Guide for setup.
Supported Resources
Radar auto-discovers any CRD in your cluster. Popular tools get dedicated integrations with topology edges, detail views, and AI summaries.
| Category | Resources |
|---|---|
| Workloads | Deployments, DaemonSets, StatefulSets, ReplicaSets, Pods, Jobs, CronJobs |
| Networking | Services, Ingresses, NetworkPolicies, Endpoints, PodDisruptionBudgets |
| Configuration | ConfigMaps, Secrets (names only, values hidden) |
| Storage | PersistentVolumeClaims, PersistentVolumes, StorageClasses |
| Autoscaling | HorizontalPodAutoscalers, VerticalPodAutoscalers |
| Cluster | Nodes, Namespaces, ServiceAccounts, Events |
| GitOps (FluxCD) | GitRepository, OCIRepository, HelmRepository, Kustomization, HelmRelease, Alert |
| GitOps (ArgoCD) | Application, ApplicationSet, AppProject |
| Argo Rollouts | Rollout |
| Argo Workflows | Workflow, WorkflowTemplate |
| cert-manager | Certificate, CertificateRequest, Order, Challenge, Issuer, ClusterIssuer |
| Gateway API | Gateway, GatewayClass, HTTPRoute, GRPCRoute, TCPRoute, TLSRoute |
| Istio | VirtualService, DestinationRule, Gateway, ServiceEntry, PeerAuthentication, AuthorizationPolicy |
| Traefik | IngressRoute, IngressRouteTCP, IngressRouteUDP, Middleware, MiddlewareTCP, TraefikService, ServersTransport, ServersTransportTCP, TLSOption, TLSStore |
| Contour | HTTPProxy |
| Knative Serving | Service, Configuration, Revision, Route, DomainMapping |
| Knative Eventing | Broker, Trigger, EventType, Channel, InMemoryChannel, Subscription |
| Knative Sources | PingSource, ApiServerSource, ContainerSource, SinkBinding |
| Knative Flows | Sequence, Parallel |
| Knative Networking | Ingress, Certificate, ServerlessService |
| Karpenter | NodePool, NodeClaim (+ provider-specific NodeClasses via auto-discovery) |
| KEDA | ScaledObject, ScaledJob, TriggerAuthentication, ClusterTriggerAuthentication |
| Prometheus Operator | ServiceMonitor, PodMonitor, PrometheusRule, Alertmanager |
| Security (Trivy) | VulnerabilityReport, ConfigAuditReport, ExposedSecretReport, ClusterComplianceReport, SbomReport, RbacAssessmentReport, InfraAssessmentReport |
| Velero | Backup, Restore, Schedule, BackupStorageLocation, VolumeSnapshotLocation |
| External Secrets | ExternalSecret, ClusterExternalSecret, SecretStore, ClusterSecretStore |
| CloudNativePG | Cluster, Backup, ScheduledBackup, Pooler |
| Kyverno | Policy, ClusterPolicy, PolicyReport, ClusterPolicyReport |
| Sealed Secrets | SealedSecret |
| Cost (OpenCost) | Namespace/workload/node cost breakdown via Prometheus (no CRDs) |
| CRDs | Any Custom Resource Definition in your cluster (auto-discovered) |
Keyboard Shortcuts
| Shortcut | Action |
|---|---|
1–6 |
Switch view (Home, Topology, Resources, Timeline, Helm, Traffic) |
t |
Toggle dark/light theme |
? |
Show keyboard shortcuts |
⌘K |
Open command palette |
/ |
Focus search (context-aware) |
f |
Fit topology to screen |
+ / - / 0 |
Zoom in / out / reset (topology) |
j / k |
Navigate rows (resources, helm) |
g g / G |
Jump to first / last row |
Enter / d |
Open selected resource detail |
y |
Open YAML view |
l |
Open logs (pods/workloads) |
[ / ] |
Previous / next resource kind |
Escape |
Close panel/modal/search |
Topology: Pan (drag), Zoom (scroll), Select (click), Multi-select (Shift+click)
Development
See the Development Guide for building from source, architecture details, API reference, and contributing.
Quick start:
git clone https://github.com/skyhook-io/radar.git
cd radar
make deps
# Terminal 1: Frontend with hot reload (port 9273)
make watch-frontend
# Terminal 2: Backend with hot reload (port 9280)
make watch-backend
Contributing
Contributions are welcome! Please read our Contributing Guide for details on the development workflow, pull request process, and coding standards.
About
Radar is built and maintained by Skyhook (YC W23) and is open source under Apache-2.0. The OSS version is fully featured and the recommended way to run Radar.
For teams that want hosted multi-cluster Radar with SSO and shared dashboards, we also offer Radar Cloud.
License
Apache 2.0 — see LICENSE
Open source. Free forever.
Built by Skyhook
Reviews (0)
Sign in to leave a review.
Leave a reviewNo results found



