sidequest
Health Warn
- License — License: MIT
- Description — Repository has a description
- Active repo — Last push 0 days ago
- Low visibility — Only 5 GitHub stars
Code Fail
- network request — Outbound network request in macOS/SideQuestAppTests/sentencepiece-fixtures.json
- rm -rf — Recursive force deletion command in macOS/scripts/build-ad-hoc.sh
- rm -rf — Recursive force deletion command in macOS/scripts/build-and-sign.sh
- eval() — Dynamic code execution via eval() in macOS/scripts/build-coreml-model.sh
- rm -rf — Recursive force deletion command in macOS/scripts/build-coreml-model.sh
- eval() — Dynamic code execution via eval() in macOS/scripts/build-embeddinggemma-tarball.sh
- rm -rf — Recursive force deletion command in macOS/scripts/build-embeddinggemma-tarball.sh
- rm -rf — Recursive force deletion command in macOS/scripts/create-dmg.sh
- network request — Outbound network request in macOS/scripts/generate-tokenizer-fixtures.py
Permissions Pass
- Permissions — No dangerous permissions requested
This is a macOS plugin and native app for Claude Code that watches your current work and surfaces contextual developer tool suggestions as native notification cards, capped at five per day.
Security Assessment
Overall risk: Medium. The tool accesses your conversation context to generate local, on-device embeddings, though it claims only anonymous IDs leave your machine. The install method pipes a remote script directly into bash (`curl | bash`), which is a common but inherently risky vector that should be audited first. Automated code scans flagged multiple dynamic `eval()` executions and several `rm -rf` recursive force deletions. However, these risky commands appear strictly contained within build and development scripts rather than the main application runtime. Outbound network requests are also present, which aligns with its need to fetch tool suggestions and run Google OAuth. No dangerous explicit system permissions or hardcoded secrets were detected.
Quality Assessment
The project is very new and has extremely low community visibility with only 5 GitHub stars. Despite this, it is actively maintained, with repository pushes occurring as recently as today. It benefits from clear documentation, a permissive MIT license, and a commendable focus on security transparency—providing a dedicated build verification file (BUILD.md) so users can check SHA256 hashes and review the source before running anything.
Verdict
Use with caution: while the tool is open and actively maintained, its low community adoption, contextual data access, and flagged build scripts mean you should thoroughly audit the install script and source code before deploying it in sensitive environments.
Contextual dev-tool discovery for Claude Code. The right tool, right when you need it. macOS plugin + native app.

Contextual dev-tool discovery for Claude Code
Install · Quests · Privacy · Verify Build · Issues



SideQuest watches what you're working on inside Claude Code and surfaces one contextual dev-tool suggestion when it actually fits — a native macOS card you can dismiss with a keystroke, capped at 5 a day. No feed. No email. No LLM mediation. Conversation content stays on your machine; matching runs on anonymous IDs and on-device embeddings.
Install
curl -fsSL https://get.trysidequest.ai/install.sh | bash
Installs the plugin into Claude Code, downloads the native macOS notification app, and runs Google OAuth (browser opens). macOS 13+ required.
That's it. Quests appear when context says they're useful.
Auditing the install script? See BUILD.md — covers source review, SHA256 verification against the repo copy, and release-tag pinning.
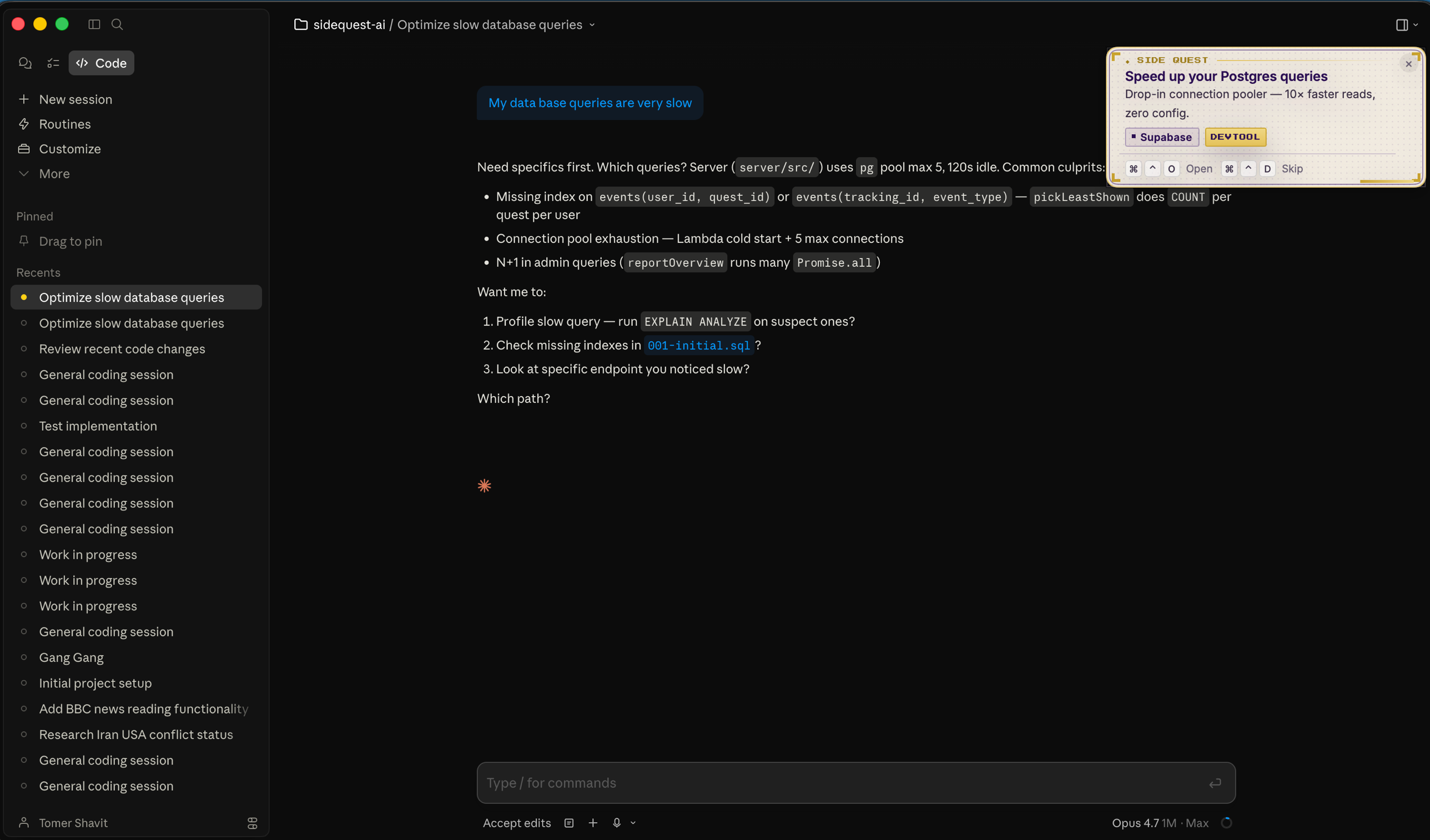
A quest fires in the corner of Claude Code Desktop. Native, dismissable, capped at 5/day.
Why SideQuest
- Right tool, right moment. While you're debugging Postgres, get a pointer to a faster connection pooler. Not a feed. Not a newsletter. A timed nudge inside the editor where you already are.
- Native, not LLM-mediated. Quests render through a real macOS notification card via the SideQuest app — 100% delivery. Doesn't depend on Claude choosing to surface anything.
- Privacy by design. Your words stay on your Mac. Only anonymous IDs and a local embedding of your last turn (text → numbers, on-device) reach our servers. See Privacy.
- Cap-respected. Max 5/day. 20-minute cooldown. One ⌘⌃D dismiss permanently mutes. Do-Not-Disturb is one slash command away.
- Open + audit-ready. MIT. Reproducible plugin tarballs. Source-pinned binaries. See BUILD.md to verify.
Quests
Skills available inside Claude Code:
| Skill | What it does |
|---|---|
/sidequest:sq-login |
Sign in with Google. One-time. |
/sidequest:sq-status |
Health check — auth, app, API, timing. Run first when stuck. |
/sidequest:sq-settings |
Toggle the plugin on or off. |
/sidequest:sq-do-not-disturb |
Pause quests for 2 hours. |
/sidequest:sq-retrigger |
Re-show the last quest. |
/sidequest:sq-feedback |
Send feedback. |
/sidequest:sq-update |
Pull the latest plugin + app. |
/sidequest:sq-uninstall |
Remove everything. |
Privacy
What stays on your machine:
- Conversation content (Claude messages, prompts, code)
- Project files, repo contents, file paths
- Anything Claude reads or writes
What we send to the API (only when a quest fires):
- Anonymous user ID (UUID, not your email)
- Anonymous session/tracking ID (UUID per quest)
- Anonymous tag IDs (e.g.
tag_4791— never the source string) - An on-device embedding of your last turn — your text is turned into a list of numbers locally on your Mac; only those numbers leave, never the words
- Quest engagement: shown / clicked / dismissed
- Plugin + app version (for compatibility checks)
Storage on your machine:
~/.sidequest/config.json— auth token, settings~/.sidequest/timing-state.json— quest cap state~/.sidequest/tech-context.json— anonymized tag IDs~/.sidequest/sidequest.sock— Unix socket (plugin ↔ app)
Code paths to inspect:
- Outbound network calls:
plugin/hooks/stop-hook - On-device embedding (where text becomes numbers):
macOS/SideQuestApp/Models/EmbeddingModel.swift - Tag anonymization:
plugin/hooks/extract-context.py
How it works
Plugin (Claude Code hook). A stop-hook and session-start hook. Pulls anonymous tag IDs from your project context and hands your last turn to the native app for on-device embedding, then asks the API for the matching quest and passes it back to the app to display. Source: plugin/hooks/.
Native app (macOS). Embeds your last turn locally — text in, numbers out, words never leave the app. Renders each quest as a native floating card, top-right. Handles open/skip keyboard. Auto-launches at login. Source: macOS/.
API. Takes the anonymous IDs + the on-device embedding, returns one quest from the catalog. Never sees your prompt content.
Updates + uninstall
Updates are silent. The session-start hook compares your installed plugin/app version against the latest published version and pulls the new tarball/DMG when they differ.
To remove everything:
curl -fsSL https://get.trysidequest.ai/uninstall.sh | bash
Or, in Claude Code:
/sidequest:sq-uninstall
Verify the build
This repo publishes deterministic plugin tarballs and source-pinned macOS DMGs. Anyone can clone at a release tag, rebuild, and confirm the SHA256 matches the asset on GitHub Releases. See BUILD.md for the step-by-step verification guide.
Support
- Run
/sidequest:sq-statusfor a self-diagnosis. - Open an issue for bugs or feature requests.
License
MIT — see LICENSE.
Reviews (0)
Sign in to leave a review.
Leave a reviewNo results found